Fraudulent Immigration Scam
What’s on this page
Global Fraudulent Scheme Targeting National Immigration Services
Overview
CTM360 has identified a fraudulent scheme involving fake websites targeting National Immigration services globally. The deceiving campaign extends to Electronic Travel Authorization, Evisa, and Electronic Custom Declaration processes. These scams have increased dramatically as more things shifted online and require less paperwork. Scammers take advantage of this by making fake websites. People need to be aware of this and be careful not to get tricked.
These fake websites usually use a basic web design and are hosted on well-known hosting services to look real. Additionally, these fake websites put up disclaimers in fine print stating to be private companies and have no affiliation with any government entities. By doing this, it makes it challenging for the Hosting Providers and Domain Registrars to take action on them.

CTM360 Observations
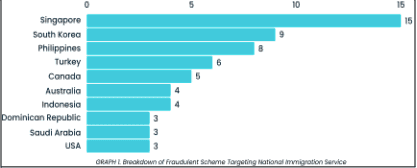
Based on our analysis of the suspicious infrastructure, we believe these fake websites are part of a broader scam campaign targeting multiple immigration services at the same time. Some of the top countries being targeted include Singapore, South Korea, the Philippines, and Turkey. We expect this scam to also occur in other countries in the near future.
The scam initiates with scammers paying for fake ads on search engines, so they show up at the top of search results. They manipulate the search engine algorithms to get their fake sites noticed more easily. This technique makes it more likely for people to accidentally find these fake websites. The ads are constructed in a way that makes the fake sites seem real, so people might trust them without realizing they're being tricked.
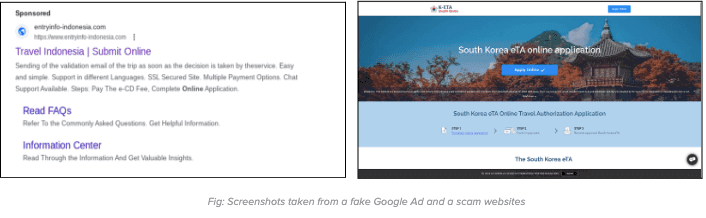
When clicking on the fake ad, users will be redirected to a fake website. On the fake website, they will be prompted to initiate the online visa application process. The process found on the fake website is crafted closely to mimic the procedures found on the official website.
After entering the card details, users will be consistently displayed with error messages falsely claiming payment failures. In reality, the sensitive carding information has already been captured and submitted to the server controlled by the scammers.
Moreover, numerous countries have issued official warnings advising against such fake websites. Please refer to the following sources for more information:
- https://www.cgisf.gov.in/page/important-advisory-on-fake-indian-e-visa-websites/
- https://ircc.canada.ca/english/helpcentre/answer.asp?qnum=1233&top=16
- https://www.perthnow.com.au/news/bali/bali-scam-warning-for-aussie-travellers-to-watch-out-for-fake-websites-providing-counterfeit-visas-c-10513578
- https://www.kenyaembassyaddis.org/2021/06/fraudulent-visa-application-websites/
Recommendations
How to avoid becoming a victim of such scams
For individuals:
- Be very cautious about the sponsored ads specifically about government services.
- When applying for any travel-related services, only use the official website provided by the immigration authorities of the country you're visiting. This may require some research by individuals to ensure they have reached the genuine website.
- Be cautious about clicking on suspicious web URLs, even if they seem to come from people you know.
For Government agencies, ISPs and Domain Registrars:
- Government service providers should publish a list of authorized agents on their websites. This will enable end-users to verify the right provider. Furthermore, it will also provide evidence for the Domain registrar to take prompt action.
- Government agencies are advised to regularly monitor such fake websites that do not have any authorization from the government and update the list of these fake websites on their official portal.
- Government agencies should actively engage with security vendors to identify and take down these fake websites and fake ads.
- There should be national procedures for Local ISPs and National CERTs to block such websites once notified by the right authorities.
Recent Blogs
Microsoft Joins the Push: DMARC Mandatory for High-Volume Senders Starting May 2025
Overview
The fight against email-based threats is intensifying. Following the lead of Google and Yahoo, Microsoft has officially announced the mandatory implementation of email authentication protocols, SPF, DKIM, and DMARC, for high-volume email senders, effective May 5, 2025. Domains sending over 5,000 daily emails to Microsoft's platforms, including Outlook.com, Hotmail.com, and Live.com, will be required to authenticate their messages. Initially, non-compliant messages will be redirected to recipients' Junk folders, with eventual total rejection expected if compliance isn't achieved. This enforcement represents a critical step in securing global email communications from spoofing and phishing threats (Microsoft Tech Community).
Understanding Email Authentication
Email authentication has become essential in combating increasingly sophisticated phishing and spoofing attacks. Three core standards have been adopted widely:
- Sender Policy Framework (SPF: RFC 7208): Verifies the legitimacy of the sending mail server, ensuring messages originate from authorized infrastructure. SPF helps prevent sender address forgery by defining authorized sending sources in DNS records.

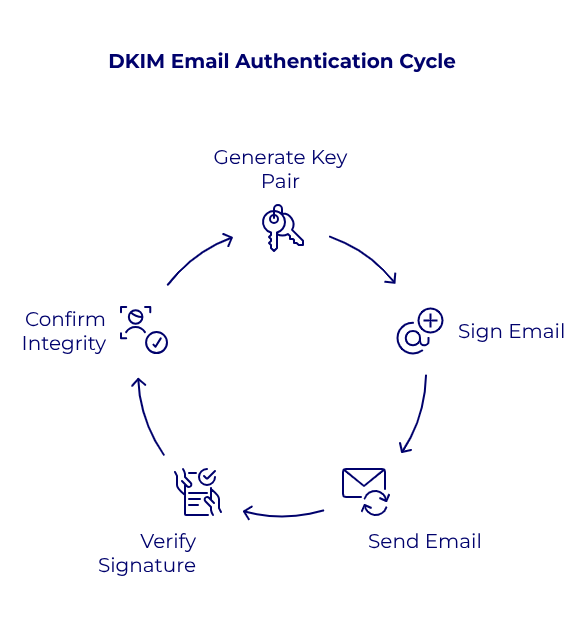
- DomainKeys Identified Mail (DKIM: RFC 6376): Cryptographically signs email messages, allowing recipients to confirm message content hasn't been altered in transit. DKIM leverages public-private key pairs to ensure message integrity and authenticity.
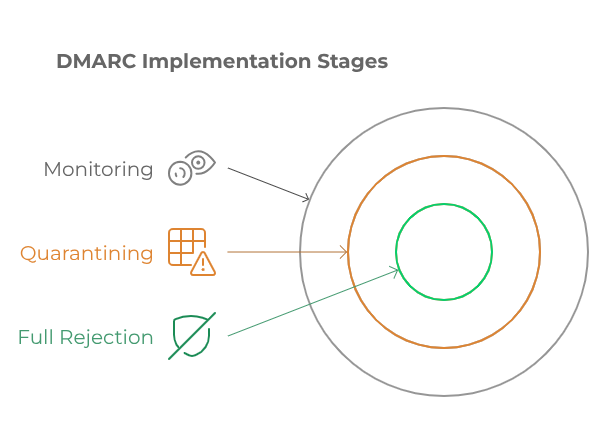
- Domain-based Message Authentication, Reporting, and Conformance (DMARC: RFC 7489): Combines SPF and DKIM to enforce domain alignment, verify authenticity, and provide reporting mechanisms for senders to track email usage and potential abuse. DMARC is recommended to be implemented in three incremental stages: initial monitoring (p=none), intermediate quarantining of suspicious messages to test the policy impact (p=quarantine), and full rejection of unauthorized emails to achieve DMARC compliance (p=reject).
Email Content and Delivery Best Practice Guidance
To help the email ecosystem thrive and ensure that legitimate communications reach users' inboxes, major providers like Google, Yahoo, and Microsoft have released a unified set of technical and content-based requirements. This section consolidates these guidelines into a single resource for senders seeking to avoid spam filtering and maintain high deliverability rates.
1. Message Headers & Structural Integrity
2. Content Hygiene and Formatting
3. Infrastructure and Technical Configuration
4. Recipient List Management
5. Engagement and Complaint Monitoring
6. Summary Recommendations
- Align headers and domains with clear, professional identities.
- Respect opt-in and unsubscribe behaviors with transparent mechanisms.
- Structure content to be clean, concise, and free of deceptive or spammy characteristics.
- Maintain technical hygiene through DNS, TLS, SPF limits, and ARC usage.
- Monitor sender reputation and user engagement continuously.
Immediate Impact and Risks of Non - compliance
As of May 2025, domains that fail SPF or DKIM checks or lack a correctly configured DMARC policy with alignment will risk having their emails marked as spam or not delivered at all. Misalignment occurs when the domain used in the message's "From" address doesn't match the domains authenticated by SPF or DKIM.
Organizations failing to comply face significant risks, including diminished deliverability rates, compromised customer trust, and increased susceptibility to impersonation attacks. These impacts directly affect an organization's reputation, customer engagement, and potentially, its revenue.
Actionable Recommendations for Immediate Implementation
To effectively prepare for these mandatory standards, organizations should:
- Audit current DNS records: Utilize tools such as "dig" or Google DNS to verify SPF, DKIM, and DMARC records.
- Begin with Monitoring (p=none): Initially deploy DMARC in monitoring mode to understand email flows and detect anomalies without risking legitimate email delivery.
- Gradually enforce stricter policies: Move from quarantine to full rejection while monitoring.
- Ensure domain alignment: "From" domain must match what’s authenticated via SPF or DKIM.
- Maintain email hygiene: Clean lists, include a clear opt-out option, and avoid using misleading subject lines or headers.
Start Your DMARC Journey with CTM360 Free Community Edition
To support organizations navigating these changes, CTM360 offers a complimentary zero-cost Community Edition platform. It allows comprehensive monitoring, management, and enhancement of your DMARC records and email authentication setup. This proactive approach helps organizations reduce risks associated with impersonation attacks and maintain reliable email communication.
Join CTM360 Community Edition today, no hidden costs, simply real security.
Reference:
Disclaimer:
The information contained in this document is meant to provide general guidance and brief information to the intended recipient pertaining to the incident and recommended action. Therefore, this information is provided "as is" without warranties of any kind, express or implied, including accuracy, timeliness, and completeness.
Consequently, under NO condition shall CTM360®, its related partners, directors, principals, agents, or employees be liable for any direct, indirect, accidental, special, exemplary, punitive, consequential, or other damages or claims whatsoever including, but not limited to loss of data, loss in profits/business, network disruption...etc., arisina out of or in connection with this advisory.
For more information: Email: monitor@ctm360.com Tel: (973) 77 360 360

Securing Browsing Extensions
Summary:
In December 2024, hackers compromised at least 35 Google Chrome extensions, affecting approximately 2.6 million users. The attack exploited phishing emails sent to developers, masquerading as Google policy violation notices. These emails tricked developers into granting permissions to a malicious OAuth application named
“Privacy Policy Extension.
” Once authorized, the attackers gained control over the extensions, injecting malicious code to steal user data, particularly targeting Facebook credentials and business accounts. Browser extensions can significantly enhance productivity by adding new features to web browsers like Microsoft Edge and Google Chrome. However, they also pose significant security risks, as malicious or compromised extensions can lead to data breaches, malware infections, and unauthorized access to corporate networks. It is crucial for organizations to control, block, or manage browser extensions to minimize security risks, particularly in an enterprise environment. This advisory outlines the steps to block and protect browser extensions for Microsoft Edge and Google Chrome, and it also includes specific guidance on managing extensions using Microsoft Intune.
Risks Associated With Browser Extensions
● Data Exposure: Some extensions can access sensitive data (e.g., browsing history, credentials, and files), potentially exposing confidential information.
● Malicious Extensions: Cybercriminals can create or compromise extensions, making them a vector for malware distribution or data exfiltration.
● Phishing Risks: Extensions may manipulate web content, tricking users into providing sensitive information.
● Performance Degradation: Some poorly coded extensions can slow down browsers or degrade system performance.
Managing Browser Extensions Using Group Policy
A. Microsoft Edge
Using Group Policy (Windows)
1. Open the Group Policy Management Console (GPMC).
2. Navigate to: Computer Configuration > Administrative Templates > Microsoft Edge > Extensions
3. Set the following policies:
a. Control which extensions are installed silently: Specify allowed extensions by adding their extension IDs.
b. Configure extension management settings: T o block all extensions, set this policy to "*" (deny all).
c. Configure the list of force-installed extensions: If any extension is necessary for business, add the corresponding extension ID here.
B. Google Chrome
Using Group Policy (Windows)
1. Open the Group Policy Editor.
2. Navigate to: Computer Configuration > Administrative Templates > Google > Google Chrome > Extensions
3. Set the following policies:
a. Block external extensions: Set the policy to block all extensions unless specifically allowed by adding the extension IDs.
b. Configure extension install allow list: If certain extensions are necessary, add their extension IDs here.
c. Configure extension install blocklist: Add a wildcard"*" to block all extensions.
Managing Browser Extensions Using Microsoft Intune
Organizations using Microsoft Intune for endpoint management can apply policies to control browser extension installations across all managed devices. This approach is particularly useful for managing large numbers of endpoints efficiently.
Blocking Extensions in Microsoft Edge Using Intune
1. Sign in to Microsoft Endpoint Manager Admin Center.
2. Navigate to: Devices > Configuration profiles > Create profile
3. Choose:
a. Platform: Windows 10 and later.
b. Profile type: Settings catalog.
4. In the Configuration settings, search for Extensions under Microsoft Edge:
a. Allow specific extensions to be installed (User): Specify allowed extension IDs
b. Control which extensions cannot be installed (User): Add a wildcard"*" to block all extensions.
5. Assign this profile to your target groups (specific users or devices).
Blocking Extensions in Google Chrome Using Intune
1. Sign in to Microsoft Endpoint Manager Admin Center.
2. Navigate to: Devices > Configuration profiles > Create profile
3. Choose:
a. Platform: Windows 10 and later.
b. Profile type: Settings catalog.
4. In the Configuration settings, search for Extensions under Google Chrome\Extensions:
a. Configure extension installation allow list (User): Specify allowed extension IDs
b. Configure extension installation blocklist: Add a wildcard"*" to block all extensions.
5. Assign this profile to your target groups (specific users or devices).
Note: These steps are mentioned for user-based controls. Similar configuration steps can be applied for device-based controls.
Best Practices for Managing Browser Extensions
● Audit Extensions Regularly: Regularly audit the extensions installed on users’ browsers to detect unauthorized or risky extensions.
● User Training: Educate users about the risks associated with browser extensions and how to identify malicious ones.
● Implement a Zero-Trust Model: Always assume that extensions can potentially be compromised. Apply the principle of least privilege when granting extension permissions.
● Use Security Solutions: Consider deploying security solutions that can monitor and block malicious browser activities, including suspicious extension behavior.
Conclusion
Controlling browser extensions in Microsoft Edge and Google Chrome is a critical aspect of securing enterprise endpoints. By implementing the steps outlined above, organizations can significantly reduce the risks associated with browser extensions. Whether you manage your endpoints using Group Policy or Microsoft Intune, these controls can help protect your network from potential extension-related threats. By following this advisory, organizations can take proactive steps to mitigate browser extension risks, enhancing their overall cybersecurity posture.
Reference:
https://www.bleepingcomputer.com/news/security/new-details-reveal-how-hackers-hijacked-35-google-chrome-extensions/
https://learn.microsoft.com/en-us/defender-endpoint/manage-profiles-approve-sys-extensions-intune
https://gbhackers.com/malicious-editthiscookie-extension/#google_vignette
Disclaimer
The information contained in this document is meant to provide general guidance and brief information to the intended recipient pertaining to the incident and recommended action. Therefore, this information is provided "as is" without warranties of any kind, express or implied, including accuracy, timeliness, and completeness. Consequently, under NO condition shall CTM360®, its related partners, directors, principals, agents, or employees be liable for any direct, indirect, accidental, special, exemplary, punitive, consequential, or other damages or claims whatsoever including, but not limited to: loss of data, loss in profits/business, network disruption…etc., arising out of or in connection with this advisory.
For more information:
Email: monitor@ctm360.com Tel: (+973) 77 360 360

CXO Fraud - Scam Emails Originating From Virgin Media, Optimum And Cox.Net
There is an ongoing scam email campaign targeting executives from prominent organizations around the world. These reported email addresses on the domains are genuine email accounts of 'Virgin Media', 'Optimum' & 'Cox communications' users' which are compromised and sold on underground forums. Scammers buy and use such accounts as they have a higher reputation compared to newly created free accounts to bypass email gateways and spam filters and also lower their risk of being detected or tracked back in a bigger BEC attack.
These accounts are compromised by threat actors via phishing emails and malware, and the issue with such accounts will persist as long as end users are not careful enough while dealing with phishing and malicious emails. Based on our previous experience in response with the hosts Virgin Media, Optimum and Cox.net which are TV and cable providers in the UK and USA. They do not investigate email accounts reported to their abuse team without the original email and header information as this is a mandatory requirement as per their abuse policies. However, once this information is provided they do take action by resetting/recovering the reported account of the original user.
Additionally, enabling strict quarantine measures on your email gateway from these domains will make you a harder target and eventually the attackers moving on to another one.
RECOMMENDATIONS
- As a precautionary measure, all email from private and/or external email addresses which contain the name of your executive staff in the "From" field may flagged.
- As part of containment, please ensure to quarantine emails from the domain @virginmedia[.]com, @optimum[.]net, @optonline[.]net, @cox[.]net, @cox[.]com
- As this type of email is tricky, it is highly recommended to conduct phishing awareness training for all employees to avoid potential risks.



