Content
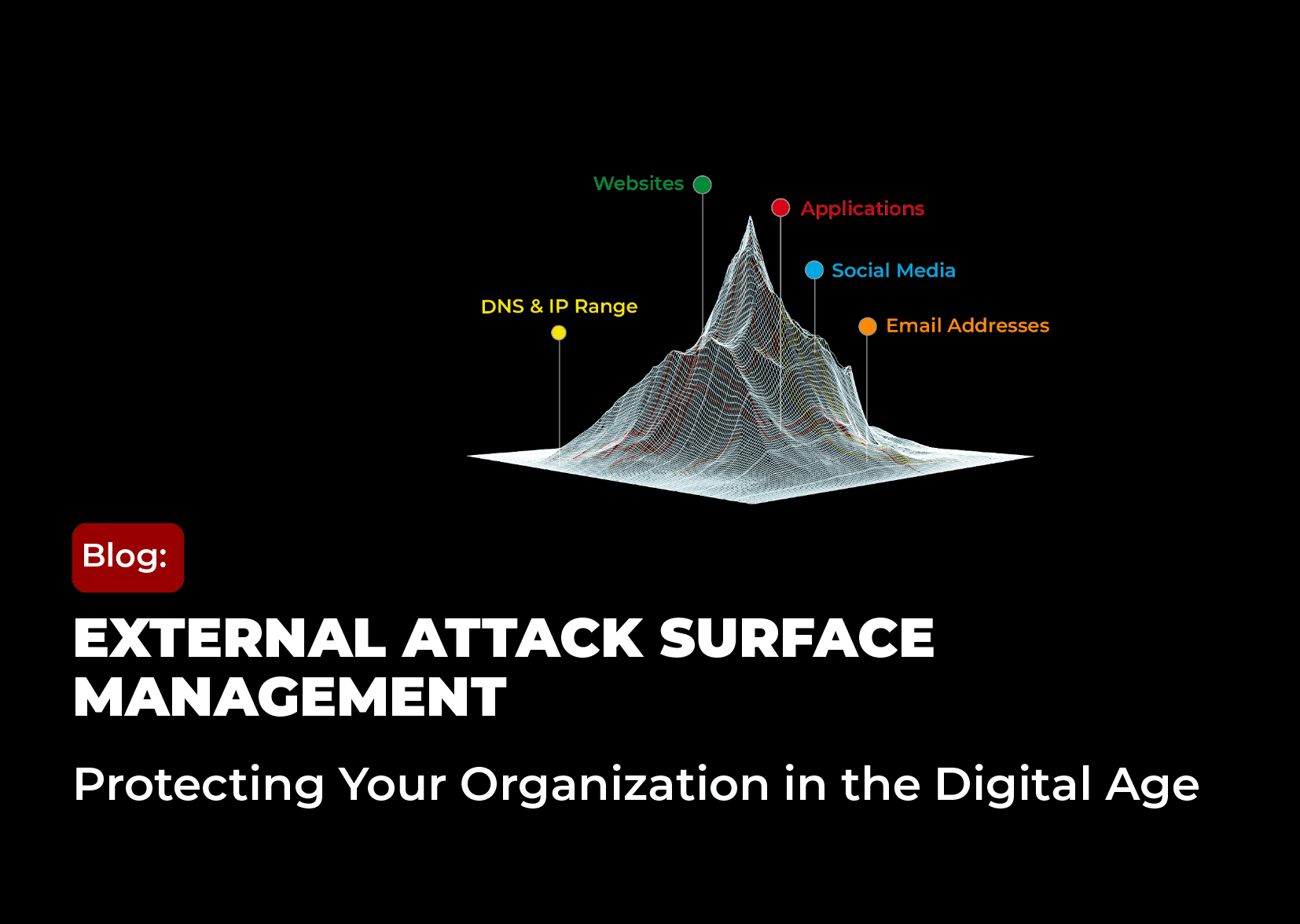
In an increasingly interconnected digital world, organisations face a growing number of cyber threats. As businesses expand their online presence, their attack surface increases, making it more vulnerable to cyberattacks. This is where External Attack Surface Management (EASM) comes into play.
09 Oct 2024
In this blog, we will explore the concept of EASM, what it includes, its importance, how it differs from security ratings, and what the future holds for this crucial aspect of cybersecurity. Additionally, we’ll discuss how CTM360 HackerView can help your organisation effectively manage its external attack surface.
What is EASM?
External Attack Surface Management (EASM) involves the continuous discovery, monitoring, and management of an organisation’s external-facing digital assets. These assets include websites, IP addresses, cloud services, and any other publicly accessible resources. A comprehensive EASM would also have the organisation’s mobile apps, genuine social media inventory, Executive Management profiles and more. EASM focuses on first building a comprehensive “Digital Asset Register” and next identifying vulnerabilities and potential entry points that could be exploited by malicious actors. By gaining a deep understanding of the external attack surface, organisations can proactively mitigate risks and prevent breaches before they occur.
From the management perspective, EASM is an essential component of a robust cybersecurity strategy. It enables organisations to see their digital footprint from the perspective of an attacker, allowing them to identify and secure weak points that could be targeted.
What is Included in an Organization’s Attack Surface?
An organisation’s attack surface consists of all the external-facing digital assets that could potentially be targeted by cybercriminals. These include:
An organization’s collection of domains, along with their associated hosts and sub-domains, creates numerous potential entry points for attackers. Each sub-domain may have unique vulnerabilities that can be exploited if not properly secured.
Public-facing websites and web applications are common targets for attackers seeking to exploit vulnerabilities such as outdated software or weak authentication mechanisms.
With the rise of cloud computing, organisations often use cloud-based services for data storage and processing. Misconfigurations or insufficient security measures in these services can expose sensitive information.
Public IP addresses can be scanned by attackers to identify open ports or vulnerable services that can be exploited.
Organisations often rely on third-party vendors or services that have access to their systems. These integrations can introduce additional vulnerabilities if not properly managed.SSL/TLS Certificates:
Weak or expired certificates can leave encrypted communications vulnerable to interception.
A comprehensive EASM solution would also include -
An organisation's presence on social media platforms can be targeted by attackers for impersonation or phishing attempts.
Attackers can create rogue mobile apps on third party stores to impersonate trusted brands, with the goal of gaining unauthorised access to information that can be used to commit fraudulent transactions.
Attackers may attempt to impersonate an organisation's executive leadership for social engineering attacks.
Payment card information, including BIN (Bank Identification Number) data, can be exposed and used for fraudulent activities.
The list of technologies and their respective versions visible in the organisation's attack surface can help identify potential vulnerabilities and misconfigurations.
The attack surface also includes shadow IT, which refers to information technology systems implemented by departments outside of the central IT department to circumvent the limitations and restrictions set by the central information systems.
Why is EASM Important?
EASM is critical for several reasons:
1. Technology consolidation
EASM promotes a unified security strategy, enabling organizations to consolidate their ever growing digital assets and stack of technologies and enhance the overall management of external cyber risk.
2. Reducing Attack Surface
Through continuous monitoring and assessment, EASM assists organizations in reducing their attack surface by proactively managing and securing external assets.
3. Proactive Risk Management:
EASM allows organisations to identify vulnerabilities before they are exploited. By continuously monitoring the attack surface, organisations can address security gaps promptly, reducing the likelihood of a successful attack.
4. Real-Time Visibility:
Cyber threats are constantly evolving, and new vulnerabilities emerge regularly. EASM provides real-time visibility into an organisation’s external assets, ensuring that security teams are always aware of the current state of the attack surface.
5. Regulatory Compliance:
Many industries are subject to strict regulatory requirements regarding data protection and cybersecurity. EASM helps organisations maintain compliance by ensuring that all external assets are properly secured.
6. Cost Efficiency:
Preventing a cyberattack is often far less expensive than dealing with the aftermath of a breach. EASM enables organisations to allocate resources more efficiently by prioritising the most critical vulnerabilities.
How is EASM Different from Security Ratings?
While both EASM and security ratings play a role in assessing an organisation’s cybersecurity posture, they serve different purposes and offer distinct benefits:
1. Scope of Analysis:
Security ratings are typically based on a broad assessment of an organisation’s overall security practices, often using data from public sources. EASM, on the other hand, focuses specifically on the external attack surface, providing a more detailed and targeted analysis of potential vulnerabilities.
2. Continuous Monitoring:
EASM involves continuous monitoring of external assets, offering real-time insights into the attack surface. Security ratings are often static, providing a snapshot of an organisation’s security posture at a specific point in time.
3. Actionable Insights:
EASM provides actionable insights that organisations can use to address specific vulnerabilities. Security ratings are more generalised and may not offer the same level of detail needed to implement targeted security measures.
4. Perspective:
EASM approaches cybersecurity from the attacker’s perspective, identifying entry points and weaknesses that could be exploited. Security ratings focus on the organisation’s overall security practices and controls.
What Does the Future Hold?
As cyber threats continue to evolve, the importance of EASM will only grow. Organisations are increasingly adopting digital transformation strategies, expanding their digital footprints, and moving more services to the cloud. This expansion introduces new vulnerabilities, making EASM an essential component of any comprehensive cybersecurity strategy.
In the future, we can expect EASM tools and technologies to become more sophisticated, incorporating advanced AI and machine learning algorithms to identify and mitigate risks more effectively. The integration of EASM with other cybersecurity solutions, such as Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR), will provide organisations with a more holistic approach to managing their security posture.
How Can CTM360 HackerView Help?
CTM360’s HackerView is an innovative External Attack Surface Management (EASM) platform designed to give organisations a comprehensive understanding of their digital presence from an attacker’s perspective. By combining automated asset discovery, issue identification, remediation guidelines, security ratings, and third-party risk management, HackerView empowers businesses to proactively defend against potential cyber threats.
Here’s how CTM360 HackerView can significantly enhance your organisation's cybersecurity strategy:
1. Continuous & Automated Digital Asset Discovery
One of the most critical aspects of EASM is the ability to identify and map all external-facing digital assets. HackerView excels in this area by automatically discovering and mapping your organisation’s digital footprint. Operating in a passive and non-intrusive manner, it leverages data available in the public domain to uncover assets that may otherwise be overlooked.
The platform comes pre-populated, ensuring that from the moment you start using it, you have a comprehensive view of your digital assets. This includes websites, IP addresses, cloud services, and more. Automated discovery ensures that no asset is left unmonitored, reducing the risk of shadow IT and other unsecured entry points.
One of the key advantages of HackerView is how often it continuously discovers, updates, and refreshes all assets belonging to the organisation. The platform automatically updates its inventory of digital assets every 24-48 hours, ensuring that your security team has access to the most current and complete information about your attack surface.
2. Comprehensive Digital Risk Scorecard
HackerView provides a detailed digital risk scorecard that assesses your organisation’s visible cyber vulnerabilities. This scorecard is essential for understanding your current security posture and identifying areas that require immediate attention. The scorecard is updated continuously, allowing you to track improvements or new risks as they emerge.
3. Detailed Inventory of Digital Assets
Understanding what you have is the first step toward protecting it. HackerView provides a detailed inventory of your digital assets, allowing you to keep track of all external-facing resources. This inventory is continually updated as new assets are discovered or changes are made, ensuring that your records are always accurate and up-to-6.
4. Remediation Plans & Ongoing Guidance
Identifying vulnerabilities is only half the battle; addressing them effectively is the key to maintaining a robust security posture. HackerView not only identifies issues but also provides detailed remediation plans and ongoing guidance. These plans are tailored to your specific vulnerabilities, offering step-by-step instructions on how to address each issue.
5. Third-Party Risk Monitoring
In today’s interconnected world, organisations rely heavily on third-party vendors and partners. However, these relationships can introduce additional risks if not properly managed. HackerView’s third-party risk monitoring feature allows you to assess the security posture of your vendors, partners, and other third parties with whom you share data or systems.
6. Pre-built and Custom Portfolios
The platform allows you to access pre-built portfolios that include entities from important industry sectors within your geographic region. This allows you to benchmark your organisation's cybersecurity posture against your peers, gaining valuable insights into how you measure up. Additionally, you can create custom portfolios of your key vendors and third-party providers, continuously tracking their security health and potential vulnerabilities.
In conclusion, as organisations continue to navigate the complexities of the digital landscape, EASM will remain a vital component of cybersecurity. By leveraging advanced tools like CTM360 HackerView, businesses can protect their digital assets, stay ahead of potential threats and ensure the security of their operations.